In today’s digitally connected world, cyber threats are evolving faster than ever. Businesses are adopting cloud infrastructure, remote work environments, mobile applications, and online services at an incredible pace. While this digital transformation improves productivity and customer experience, it also opens multiple entry points for cybercriminals.
Over the last two decades of working closely with cybersecurity environments, I have seen one common mistake businesses make — they assume antivirus software alone is enough to stay secure. Unfortunately, modern cyberattacks are much more advanced.
This is exactly why organizations across industries now rely on VAPT services in India to identify hidden security gaps before hackers can exploit them.
Vulnerability Assessment and Penetration Testing (VAPT) has become one of the most important cybersecurity practices for modern enterprises. A proper VAPT audit helps businesses proactively discover weaknesses in networks, applications, servers, cloud environments, APIs, and employee security practices.
In this article, we will explore the most common cyber threats identified during VAPT audits, understand why businesses need regular security testing, and compare different cybersecurity approaches used by enterprises today.
What is VAPT?
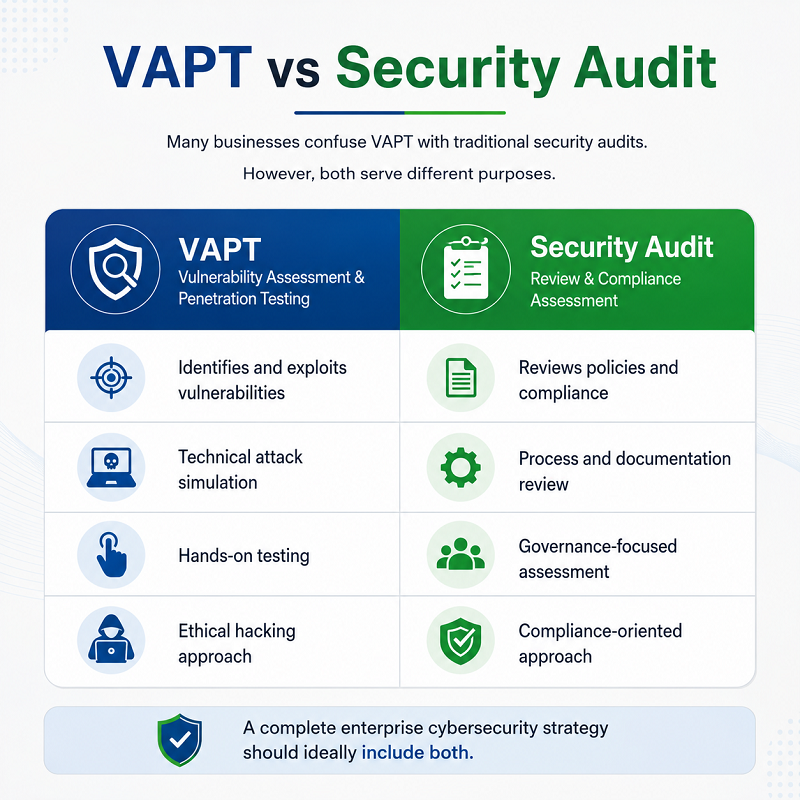
VAPT stands for Vulnerability Assessment and Penetration Testing. Although many people use the term together, both processes serve different purposes.
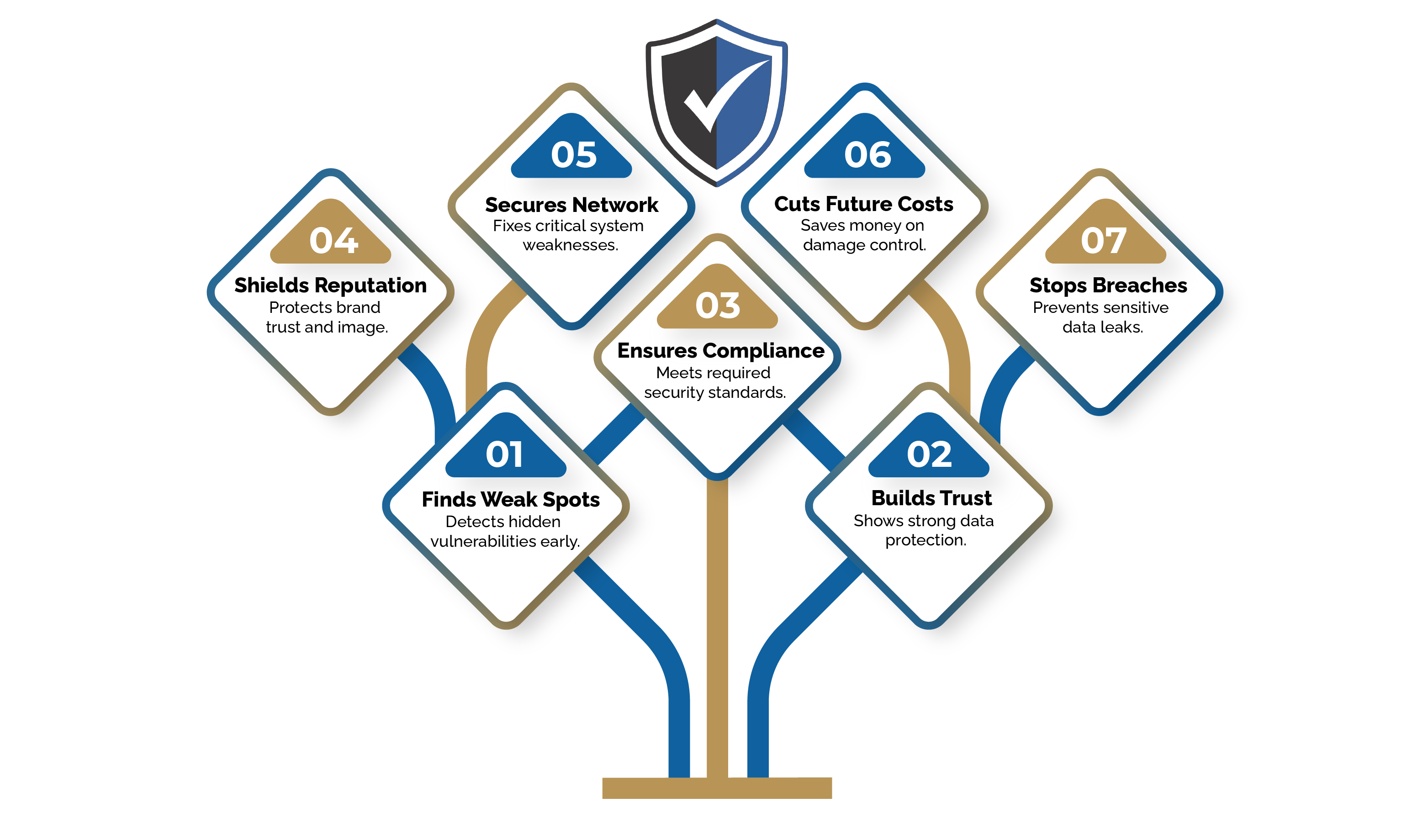
Top VAPT Advantages to Protect Your Digital Assets
Vulnerability Assessment
A vulnerability assessment focuses on identifying known security weaknesses in systems, applications, servers, databases, and networks.
This process usually includes:
- ⬩ Automated scanning
- ⬩ Configuration analysis
- ⬩ Security weakness identification
- ⬩ Risk prioritization
Penetration Testing
Penetration testing goes one step further.
Security experts simulate real-world cyberattacks to exploit identified vulnerabilities and understand their actual impact on the organization.
This process is often performed by ethical hacking services professionals who think like attackers to test the strength of business security systems.
Together, these processes form a comprehensive cybersecurity audit service that helps organizations strengthen their defenses.
Why Businesses Need VAPT Services in India
India is witnessing rapid digital growth across sectors like banking, healthcare, fintech, e-commerce, manufacturing, and government services. – Source
Unfortunately, cybercriminals are also targeting Indian businesses aggressively. – Source
Modern organizations store massive amounts of:
- ⬩ Customer information
- ⬩ Banking data
- ⬩ Financial transactions
- ⬩ Employee records
- ⬩ Intellectual property
- ⬩ Cloud data
A single vulnerability can lead to ransomware attacks, financial fraud, or large-scale data breaches.
This is why businesses increasingly partner with a trusted VAPT audit company to conduct regular:
- ⬩ Network security assessment
- ⬩ Application security testing
- ⬩ Data security assessment
- ⬩ Cyber risk assessment services
- ⬩ Managed cybersecurity services
Common Cyber Threats Identified During VAPT Audits
Let us now explore the most common vulnerabilities and cyber threats discovered during enterprise VAPT audits.
1. Weak Passwords and Poor Authentication
Weak passwords remain one of the biggest cybersecurity problems worldwide.
During IT security audits, security teams often discover:
- ⬩ Default passwords
- ⬩ Reused credentials
- ⬩ Weak password policies
- ⬩ Lack of multi-factor authentication (MFA)
Hackers use automated tools to crack weak passwords within minutes.
Poor authentication controls can allow attackers to gain unauthorized access to:
- ⬩ Banking systems
- ⬩ Employee accounts
- ⬩ Cloud dashboards
- ⬩ Customer databases
Modern VAPT services help businesses strengthen authentication systems using:
- ⬩ MFA implementation
- ⬩ Password policy enforcement
- ⬩ Identity access management
- ⬩ Privileged access control
2. Unpatched Software and Outdated Systems
Outdated software creates major security risks.
Many organizations delay critical security updates because of operational concerns or lack of monitoring.
During vulnerability assessment services, experts frequently identify:
- ⬩ Old operating systems
- ⬩ Vulnerable web servers
- ⬩ Unpatched plugins
- ⬩ Unsupported applications
Hackers actively target these known vulnerabilities because exploit codes are easily available online.
Regular security vulnerability testing helps organizations identify outdated systems before attackers do.
Did You Know?
A large percentage of ransomware attacks globally exploit already known vulnerabilities for which security patches were available months earlier.
3. Web Application Security Vulnerabilities
Today, almost every business relies on websites, portals, mobile apps, or cloud-based applications.
Unfortunately, web applications are among the most targeted attack surfaces.
During web application security testing, common issues identified include:
- ⬩ SQL Injection
- ⬩ Cross-Site Scripting (XSS)
- ⬩ Broken Authentication
- ⬩ Insecure APIs
- ⬩ Session Hijacking
- ⬩ Misconfigured Security Headers
These vulnerabilities can allow attackers to:
- ⬩ Steal customer information
- ⬩ Access sensitive databases
- ⬩ Deface websites
- ⬩ Execute malicious code
- ⬩ Bypass login systems
This is why application security testing is extremely important for organizations handling customer data.
4. Misconfigured Cloud Infrastructure
Cloud adoption is growing rapidly across Indian enterprises.
However, improperly configured cloud environments are becoming a serious security concern.
During cloud infrastructure VAPT audits, experts often identify:
- ⬩ Publicly exposed storage buckets
- ⬩ Weak access controls
- ⬩ Open management ports
- ⬩ Insecure cloud APIs
- ⬩ Poor identity permissions
Cloud misconfigurations can accidentally expose confidential customer data to the internet.
This is particularly dangerous for banking, fintech, and healthcare organizations.
5. Network Security Weaknesses
Network vulnerabilities remain one of the most common issues discovered during network security assessments.
These include:
- ⬩ Open ports
- ⬩ Weak firewall rules
- ⬩ Unsecured remote access
- ⬩ Poor network segmentation
- ⬩ Vulnerable VPN configurations
Attackers often exploit weak network configurations to move laterally inside enterprise environments.
Once inside, they can compromise multiple systems silently.
A proper penetration testing company simulates these attack paths to identify how far an attacker can penetrate business networks.
6. Social Engineering and Phishing Attacks
Not all cyberattacks target technology directly.
Many attackers target employees instead.
During social engineering VAPT exercises, ethical hackers simulate phishing attacks to test employee awareness.
Common findings include:
- ⬩ Employees clicking fake links
- ⬩ Sharing credentials unknowingly
- ⬩ Downloading malicious files
- ⬩ Falling for impersonation scams
Even highly secure organizations can become victims if employees are not trained properly.
Cybersecurity is not only about technology — human awareness is equally important.
Did You Know?
Phishing attacks continue to be one of the leading causes of enterprise data breaches worldwide because attackers exploit human trust rather than technical weaknesses.
7. Insecure Mobile Applications
Mobile apps have become critical business tools.
However, insecure mobile applications can expose:
- ⬩ Customer credentials
- ⬩ Banking information
- ⬩ Personal data
- ⬩ API keys
During mobile application VAPT, experts commonly identify:
- ⬩ Insecure data storage
- ⬩ Weak encryption
- ⬩ Hardcoded credentials
- ⬩ API vulnerabilities
- ⬩ Improper session handling
Businesses offering customer-facing mobile applications must perform regular penetration testing to avoid major security incidents.
8. Database Security Vulnerabilities
Databases are among the most valuable assets for any organization.
Unfortunately, many businesses fail to secure them properly.
Database VAPT assessments often identify:
- ⬩ Weak database passwords
- ⬩ Excessive user privileges
- ⬩ Unencrypted sensitive data
- ⬩ Backup exposure
- ⬩ SQL vulnerabilities
Compromised databases can result in massive financial and reputational damage.
Real-World Banking Industry Case Study
A mid-sized banking organization in India approached a professional VAPT audit company after noticing unusual network activity within its online banking infrastructure.
The VAPT assessment identified multiple critical vulnerabilities, including:
- ⬩ Weak administrator passwords
- ⬩ Unpatched web applications
- ⬩ Insecure API endpoints
- ⬩ Misconfigured firewall rules
During penetration testing, ethical hackers successfully demonstrated how attackers could potentially gain unauthorized access to customer account data.
Fortunately, the vulnerabilities were identified before any real cybercriminals could exploit them.
After implementing recommended fixes, the bank significantly improved its cybersecurity posture, strengthened compliance readiness, and reduced security risks across its digital banking platforms.
This case clearly highlights why regular cybersecurity audit services are essential for banking institutions.
VAPT vs Security Audit
VAPT vs SOC Monitoring
SOC (Security Operations Center) monitoring focuses on continuous threat detection and incident response.
VAPT focuses on proactively identifying vulnerabilities before attackers exploit them.
In simple terms:
- ⬩ VAPT finds weaknesses
- ⬩ SOC monitoring watches for active threats
Both services complement each other.
VAPT vs Antivirus Protection
Many businesses still believe antivirus software provides complete protection.
Unfortunately, antivirus tools alone cannot detect:
- ⬩ Misconfigurations
- ⬩ Weak passwords
- ⬩ Business logic flaws
- ⬩ API vulnerabilities
- ⬩ Cloud security gaps
VAPT provides a much deeper analysis of overall security posture.
Manual vs Automated Penetration Testing
Automated scanning tools are useful for identifying known vulnerabilities quickly.
However, manual penetration testing performed by experienced ethical hackers remains essential because human experts can identify:
- ⬩ Complex attack chains
- ⬩ Business logic flaws
- ⬩ API abuse scenarios
- ⬩ Advanced exploitation paths
The best penetration testing company combines both automated and manual testing techniques.
In-house Security Testing vs Managed VAPT Services
Some organizations prefer internal security teams, while others outsource to managed cybersecurity services providers.
Managed VAPT services offer several advantages:
- ⬩ Access to experienced cybersecurity experts
- ⬩ Advanced testing tools
- ⬩ Unbiased assessments
- ⬩ Latest threat intelligence
- ⬩ Cost-effective security expertise
For many businesses, outsourcing to a trusted VAPT services provider in India proves more practical and scalable.
Navigating the VAPT Process
A professional VAPT process usually follows a structured methodology.
1. Scope Definition
Clearly identifying systems, applications, APIs, networks, and environments to be tested.
2. Vulnerability Assessment
Using automated and manual techniques to identify security weaknesses.
3. Penetration Testing
Simulating real-world attacks to exploit vulnerabilities safely.
4. Risk Analysis
Prioritizing vulnerabilities based on severity and business impact.
5. Reporting
Providing detailed reports with remediation recommendations.
6. Remediation Support
Helping businesses fix vulnerabilities and validate security improvements.
Conclusion
Cyber threats are becoming more advanced, targeted, and damaging every year. Businesses can no longer afford to rely only on traditional security tools or reactive approaches.
Regular VAPT audits help organizations proactively identify vulnerabilities, strengthen security controls, improve compliance readiness, and reduce cyber risks before attackers exploit weaknesses.
Cyberchef, a trusted brand of Techchef Group, is among the leading providers of VAPT services in India, offering advanced vulnerability assessment services, penetration testing, and cybersecurity audit services for businesses across industries.
With headquarters in Delhi and branch offices in Chennai, Mumbai, and Bengaluru, Cyberchef helps organizations secure their digital infrastructure through professional ethical hacking services, application security testing, and managed cybersecurity services.
Mr. Anish Kumar, Founder of Cyberchef, strongly recommends regular VAPT audits as a proactive step toward building a resilient cybersecurity framework capable of handling evolving cyber threats.
If your organization wants to strengthen its cybersecurity posture, protect sensitive business data, and stay ahead of cybercriminals, now is the right time to schedule a professional VAPT assessment.
Contact Cyberchef today to schedule an appointment, speak with cybersecurity experts, or call the toll-free number for a free consultation regarding your security assessment requirements.